Search This Blog
What is STEGANOGRAPHY
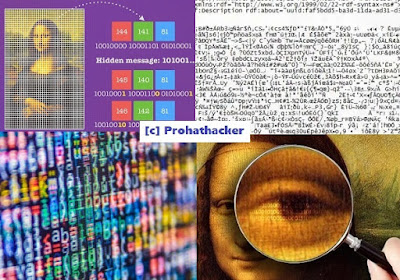
What is STEGANOGRAPHY :- Setganography is the art and science of hiding
messages and data files.The word Steganography is of Greek origin and means
"covered writing". Setganography in this process we can attach the
virus file or data file to the Text, Image, Audio, Video files. These files
known as cover file
What is Enumeration
What is Enumeration :- Obtain information about accounts, network resources
and share or other hand Enumeration is process to find out User Name, Group,
Using OS in network, open ports, network resources etc. But westart Enumeration
in target system here Hacker can make a fixed active connection to the target
system. So Hacker can hack the target then start Enumeration process.
What is Network Devices
What is Network Devices :- Computer Networking devices can communicate
two or more different network without these Devices network communication can’t
be possible.
Type of Network Devices :-
# Repeater
# Hub
# Bridge
# Switch
# Router
# Proxy
# Firewall
# Hub
# Bridge
# Switch
# Router
# Proxy
# Firewall
What is Transmission Media
Transmission
Media :- When
we create a computer network then we need to communication medium this medium
can be wired or wireless.
There
are two type of transmission media:-
# Wired medium or Guided medium.
# Wireless medium or unguided medium.
# Wired medium or Guided medium.
# Wireless medium or unguided medium.
Subscribe to:
Posts (Atom)